Objective
Help security researchers and bug bounty hunters discover exploitable instances quickly by automatically running the latest public templates from Project Discovery against a consolidated bug-bounty scope. Reduce manual steps and maintain continuous reconnaissance.
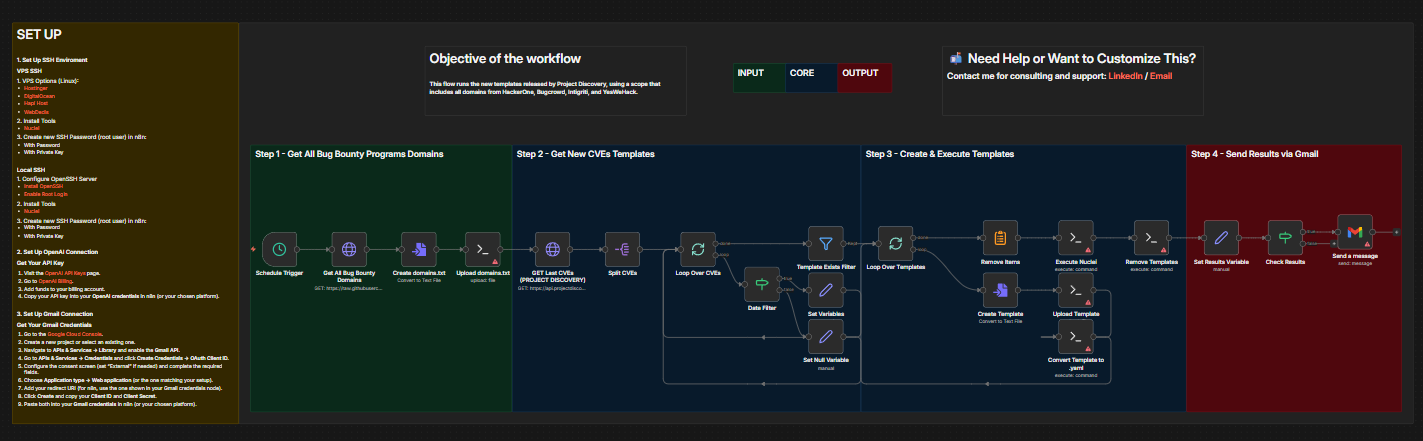
How it works
- The workflow accepts or fetches a domain list that covers HackerOne, Bugcrowd, Intigriti, and YesWeHack.
- It downloads the latest public templates from Project Discovery.
- For each new template published since the last run it: creates a file, uploads it to a remote host, and converts it to a Nuclei-compatible YAML.
- It uploads a consolidated domains wordlist to the remote host.
- It executes Nuclei with the new templates against the domains list using configured flags (concurrency, rate limits, severity tags).
- It collects and deduplicates Nuclei output.
- If results exist, it sends the findings via Gmail.
Requirements
- SSH access (root or equivalent) to a VPS or host.
- Nuclei installed on the remote host.
- Gmail OAuth2 credentials for sending notifications.
- Recommended: VPS with enough CPU and network capacity for concurrent scanning when scope is large.
![]()