2FA requirement bypass when inviting team members
Vulnerability Summary
HackerOne disclosed report --> https://hackerone.com/reports/3356149 by 0x7ashish
Summary:
The application requires users to enable 2FA before sending team invitations. However, this restriction can be bypassed by modifying client-side responses (match and replace from false to true). This allows invitations to be sent without enabling 2FA, defeating the security requirement.
Steps To Reproduce:
-
Sign up / log in to the application.
-
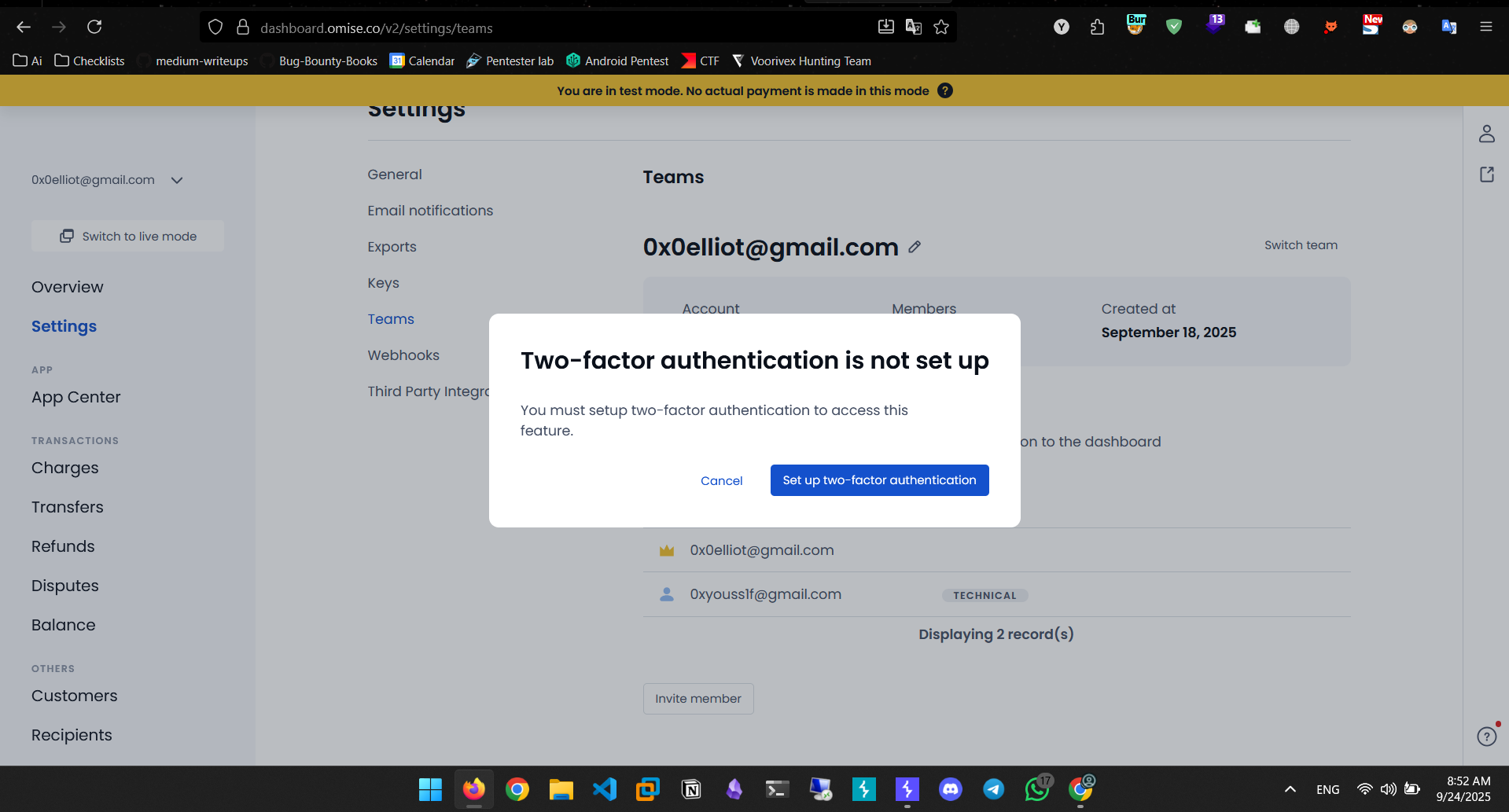
Go to the Team section.
-
Try to invite a new member → the application blocks the request, requiring 2FA.
-
Use a Burp extension ( Match and Replace) to change the client-side flag
false → true.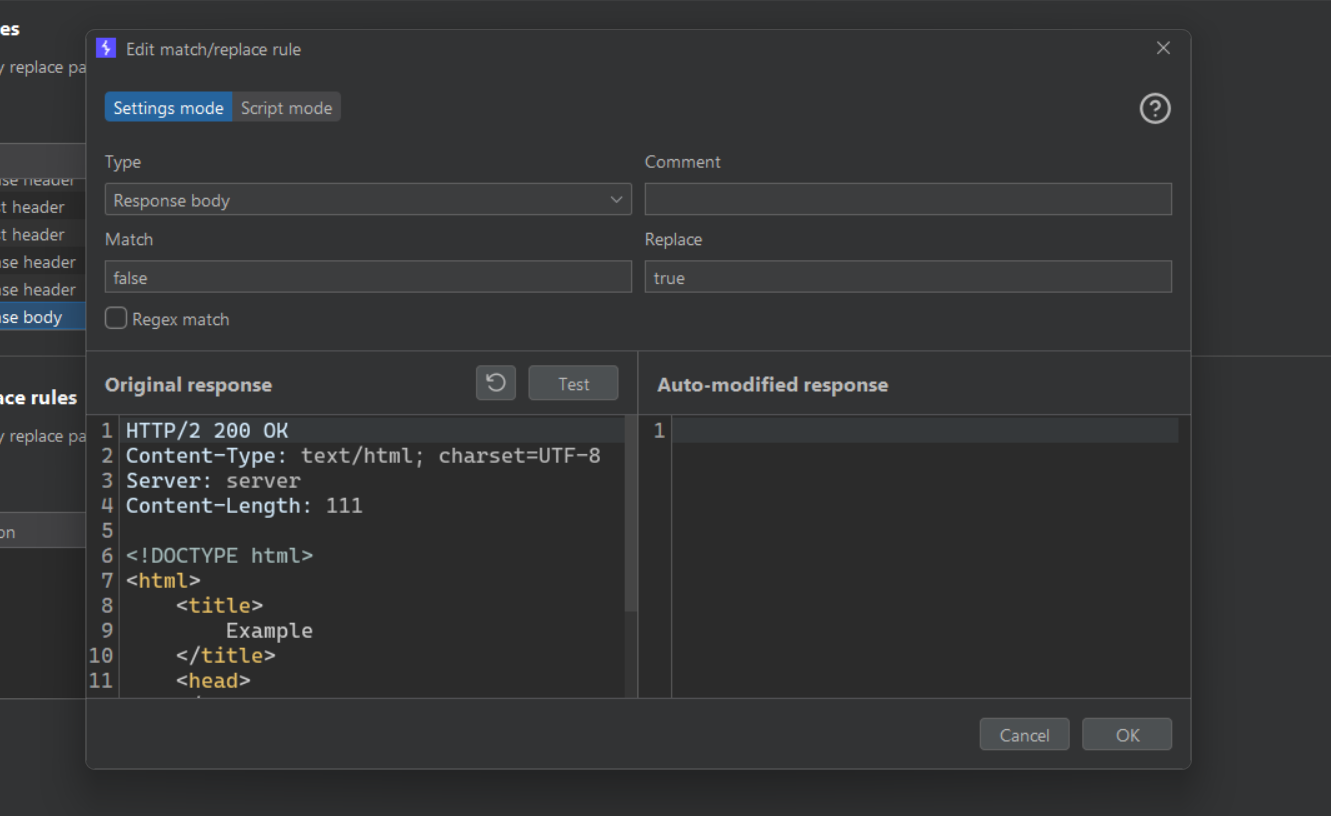
-
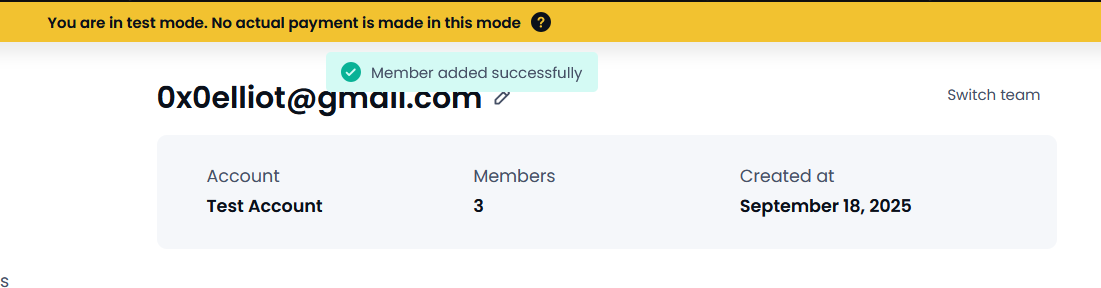
Refresh the page then attempt to send an invitation again.
-
The invitation is sent successfully without enabling 2FA.
Impact
-
This bypass allows attackers to ignore the enforced security policy.
-
Reduces the effectiveness of 2FA enforcement.
-
Could allow compromised accounts to invite unauthorized users without 2FA protection.